Cybersecurity occupation paths have become far more formal more than the several years as stability incidents have amplified and the skills expected to keep organizations harmless have turn out to be extra specialised.
A lot of of the men and women who entered the field as pc support techs or network directors with no particular teaching in stability have bolstered their capabilities over time by taking certification courses or likely again to college for a lot more education and learning.
The outcome is that the cybersecurity subject now gives distinctive job paths with milestones to be fulfilled and specifications to satisfy.
A single of the finest occupation route diagrams for security experts has been formulated by Facts Methods Security Affiliation (ISSA) Global. Termed the Cyber Protection Profession Lifecycle (CSCL), the five-action model helps aspiring and expert stability experts chart what education, working experience and certifications they will want to development.
The 5 designations in the ISSA cybersecurity occupation route model are major buckets with many discrete position titles and expertise to learn about. Here’s how the occupation path breaks down, with data on the encounter of people at every stage, the time period of time commonly linked with mastering each and every career period and the wage ranges for the work titles linked with every single degree.
Pre-Specialist: Finding started out in cybersecurity
This class pertains to persons with no cybersecurity working experience but want to get into the area. While numerous people in cybersecurity have formal computer system science training, there’s no explanation a particular person with a tunes degree or other type of liberal arts degree couldn’t go after a cybersecurity occupation.
Simone Petrella, president and co-founder of N2K and CyberVista, now N2K, stated former journalists make some of the greatest menace scientists due to the fact they have a qualifications in digging for info and producing plainly about what they have identified after investigating a subject. Men and women looking to change professions immediately after 20 decades in legislation enforcement or the army are also excellent candidates for cybersecurity. Several have worked as detectives or investigators at law enforcement departments or have received good IT and intelligence collecting expertise in the armed forces. These are all fantastic backgrounds for success in cybersecurity.
Computer system science and business students could want to pursue cybersecurity due to the fact they’ve listened to position openings and options for job advancement are considerable. Which is real, but career success hinges on having a honest fascination in the subject matter and a willingness to find and review the component of cybersecurity that most captures your desire.
Entry Stage: 1-3 a long time
Entry-level people today normally commence in pc assist or network administration, but people today with a business enterprise diploma or liberal arts degree who are doing the job on protection certifications may well also obtain on their own in entry-level employment.
A popular entry point is as an analyst in a safety functions middle (SOC). The job can be wearisome, but right after doing work 12 to 18 months in an SOC and passing some essential certifications, folks can start out searching to make the following transfer.
A phrase of warning at this juncture: Know thyself. Protection gurus recommend newcomers to pursue the part of protection that interests them most. Some men and women might in no way make great managers. They are rather palms-on varieties who work well in job-oriented situations, like penetration testing (pen tests) or threat exploration and assessment, but are not fascinated in managing persons.
Occupation titles: Associate cybersecurity analyst, associate community security analyst, cybersecurity chance analyst, SOC analyst
Education: Bachelor’s degree in company or liberal arts CompTIA Safety+
Salary array: $40,000-$80,000
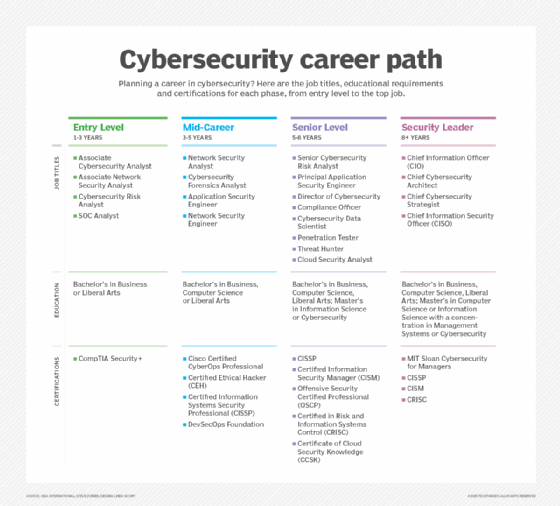
Mid-Occupation: 3-5 a long time
At this issue in their cybersecurity professions, men and women have mastered normal stability principles and have commenced branching out into the fields that fascination them.
Those who started off out in networking, for example, could have expanded their understanding and are now extra on the network safety or cloud protection architect route, when others resolved they like becoming on incident reaction teams and want to focus much more on forensics.
Even now other people might have programming backgrounds and laptop or computer science levels and have made a decision that they want to emphasis on DevSecOps, an area with superior need. This is for the reason that developers are normally focused on receiving new items out the doorway promptly, instead than on the stability of individuals goods. Programmers who have an understanding of how to make safety into the whole software lifecycle are coveted by businesses. The DevSecOps Basis is a great source.
Career titles: Community stability analyst, cybersecurity forensics analyst, software stability engineer, community protection engineer
Education: Bachelor’s degree in business enterprise, pc science, liberal arts Cisco Accredited CyberOps Expert, Certified Ethical Hacker, Qualified Information and facts Techniques Security Specialist (CISSP), DevSecOps Basis
Salary variety: $80,000-$105,000
Senior Degree: 5-8 several years
The individuals at this juncture in the cybersecurity vocation route are the kinds leading risk intelligence teams and heading up pen assessments and incident reaction teams. Several have decided that they are arms-on people who really don’t aspire to top administration and want to concentration extra on responding to situations or working with shoppers to level out vulnerabilities and produce their protection plans.
Some others just take a chance analysis keep track of and work on detailing enterprise danger to the CISO and prime administration. Some of these persons arrive from accounting backgrounds and have worked in the accounting departments of banking companies and prime money companies.
Nevertheless other individuals may well have technologies backgrounds but target far more on compliance and regulatory difficulties. They may possibly have mixed a technical history with some plan courses. For instance, anyone focused on the EU’s GDPR would require a technologies qualifications but also some track record in international business and coverage. And anyone who becomes an specialist in PCI DSS would have to have good know-how experience and a qualifications in e-commerce stability and internet enhancement and management. Cyber details researchers at this degree are increasingly expected to have know-how of AI abilities and applications.
Job titles: Senior cybersecurity possibility analyst, principal application stability engineer, director of cybersecurity, compliance officer, cybersecurity information scientist, penetration tester, menace hunter, cloud stability analyst
Schooling: Bachelor’s diploma in organization, computer system science, liberal arts master’s degree in data science or cybersecurity CISSP, Qualified Facts Security Supervisor (CISM), Offensive Protection Qualified Experienced, Certified in Danger and Info Systems Control (CRISC), Certification of Cloud Protection Information
Income selection: $105,000-$160,000 (top rated threat hunters can make shut to $250,000)
Safety Leader: 8+ yrs
Safety leaders — normally termed a main data security officer, or CISO, at big firms with a C-suite — are seasoned cybersecurity veterans with an capacity to take care of people and jobs. The finest CISOs have numerous backgrounds and can appear from strong IT coaching or even the hazard departments of banking companies. Even though some have labored in risk and compliance, other folks could have managed a handful of racks of Home windows servers and then worked in network management.
The most traditional route for an individual who wishes to come to be CISO would be to gain a laptop or computer science degree or a bachelor’s diploma in organization with a focus in IT administration. A master’s in personal computer science with a focus in cybersecurity also will help but is not essential for these with lots of a long time in the area.
 Sweet Alexander
Sweet Alexander
Candy Alexander, CISO and leader of the cybersecurity and possibility management follow at consulting firm NeuEon, explained the greatest CISOs also recognize enterprise at a deep level. Alexander, a former president of ISSA’s global board and main architect of its CSCL product, reported the sector requirements persons who can talk to senior administration in approaches they comprehend instead of talking about community logs and menace sample. Powerful CISOs can clarify what the threats are to the company and how safety incidents will impression sales, earnings, long term growth and the company’s popularity.
Other stability leader employment that pay top rated salaries consist of the pursuing:
- Main cybersecurity architect. Plans, layouts, assessments, implements and maintains stability devices.
- Main cybersecurity strategist. Models cybersecurity applications from the floor up.
Job titles: CIO, chief cybersecurity architect, chief cybersecurity strategist, CISO
Instruction: Bachelor’s degree in business, computer system science, liberal arts master’s diploma in laptop science or information and facts science with a concentration in management methods or cybersecurity MIT Sloan Cybersecurity for Managers, CISSP, CISM, CRISC
Income assortment: $160,000-$265,000 (leading persons at Fortune 500 businesses can make perfectly in surplus of $265,000)
Steve Zurier is an impartial freelance know-how author covering IT protection, networking and cloud computing.

